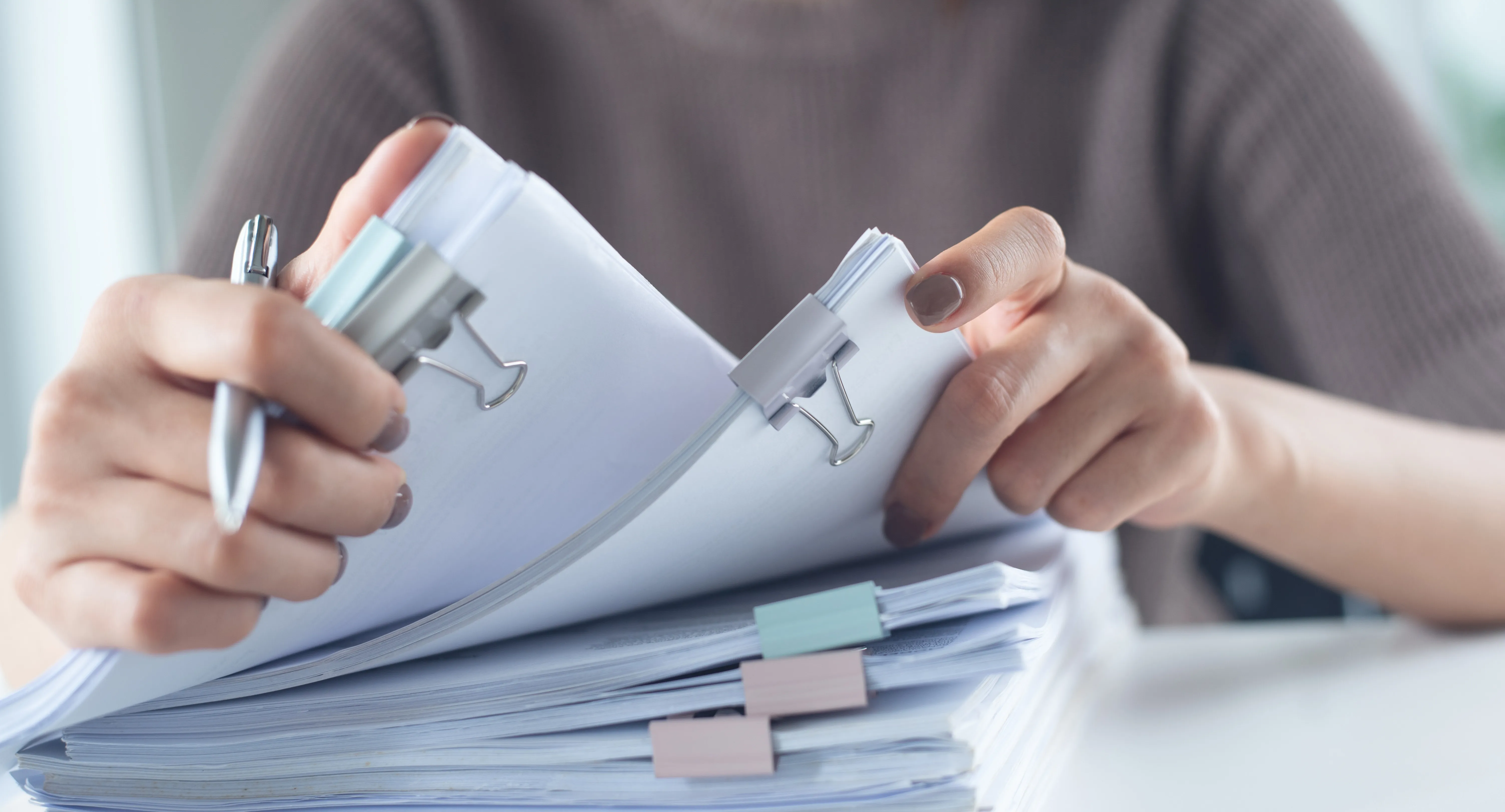
You Can’t Fight What You Can’t See
Many threats operate out of sight. Investigations 360 provides the visibility brands need by uncovering networks, supply chains, and operators behind infringements, enabling informed decisions and decisive action that addresses the root cause of brand abuse
The Challenge
Illicit networks operate across multiple channels and jurisdictions, making it difficult for brands to understand connections, identify key actors, or pinpoint the true origins of counterfeit and diversion activity.
The Solution
Network mapping uncovers physical production sites, supply routes, and key actors, providing the first hand intelligence brands need to validate risks, escalate cases, and take decisive enforcement action.
Results

.svg)
Your Window Into the Hidden Threat Landscape
The Challenge
Investigation findings are often fragmented or unclear, leaving brands without the evidence, structure, or direction needed to progress enforcement or make informed decisions.
The Solution
Actionable Reports deliver clear, verified intelligence with recommended next steps, equipping brands with the documentation, insights, and guidance required to initiate enforcement and drive meaningful outcomes.
Result

.svg)
Your Window Into the Hidden Threat Landscape
The Challenge
Infringing activity often originates offline, where manufacturers, distributors, and suppliers operate with little visibility, making it difficult to trace the true source of counterfeit or diverted goods
The Solution
Offline Source Identification uncovers physical production sites, supply routes, and key actors, providing the firsthand intelligence brands need to validate risks, escalate cases, and take decisive enforcement action.
Result

.svg)
Your Window Into the Hidden Threat Landscape
The Challenge
Legal teams often receive fragmented intelligence without the structure, evidence, or documentation needed to escalate cases. This slows enforcement, weakens outcomes, and creates inconsistent readiness across jurisdictions.
The Solution
Case File Preparation consolidates all verified intelligence, evidence, test purchase records (TPs), network mapping, HUMINT insights, and recommendations into a structured, enforcement-ready file. This ensures legal and law-enforcement partners can act decisively with minimal rework.
Result
.svg)
Your Window Into the Hidden Threat Landscape
Turn Evidence Into Action
Transform verified intelligence into clear next steps, enabling legal teams and law enforcement to act confidently and drive real disruption.

Cut through surface-level infringement with deeper visibility

Reduce internal investigative burden with Corsearch investigators doing the heavy lifting

Confidently pursue legal or regulatory enforcement with solid evidence

Preserve your brand’s reputation and revenue by tackling root sources
How It Works
Trigger
Investigation begins from a tip, flag, or pattern in platform data
Discovery
AI & analysts work together to identify actors and trace connections
Documentation
Full legal-grade case file prepared for enforcement
Action
Client pursues action via internal teams, authorities, or Corsearch partners
Reporting
Outcome and learning fed back into your Brand Protection strategy

Let’s Make Your Brand Untouchable.
Your brand deserves a trusted partner with the tools and expertise to protect your business.
Revenue Recovery
Hold infringers financially accountable for the damage.

Protect Your Domain
Protect what's yours, from registration to enforcement.

Distribution Control
Enforce channel policies and disrupt gray market sales.

CVAN
An AI that blocks non-compliant listings before publication.

Talk to an expert








.svg)
.png)





















.webp)
